CASE STUDY: Site Hacked with SEO Spam Injection - Resolved
Spam Type: Multi-niche (gambling, Japanese e-commerce, celebrity gossip) Backlinks: 2,500+ from 20+ hacked domains Status: Resolved
The Problem
The client's site was appearing in Google search results with content that had absolutely nothing to do with the actual website. Browsing the site looked completely normal. No infected files on the server, no suspicious redirects, no CMS issues. Google was indexing a completely different version of the site than what any human visitor would see.
The spam was not limited to one niche. The indexed content included:
-
Vietnamese gambling platforms (ONE88, GK88, 98WIN, M88, S666, J88)
-
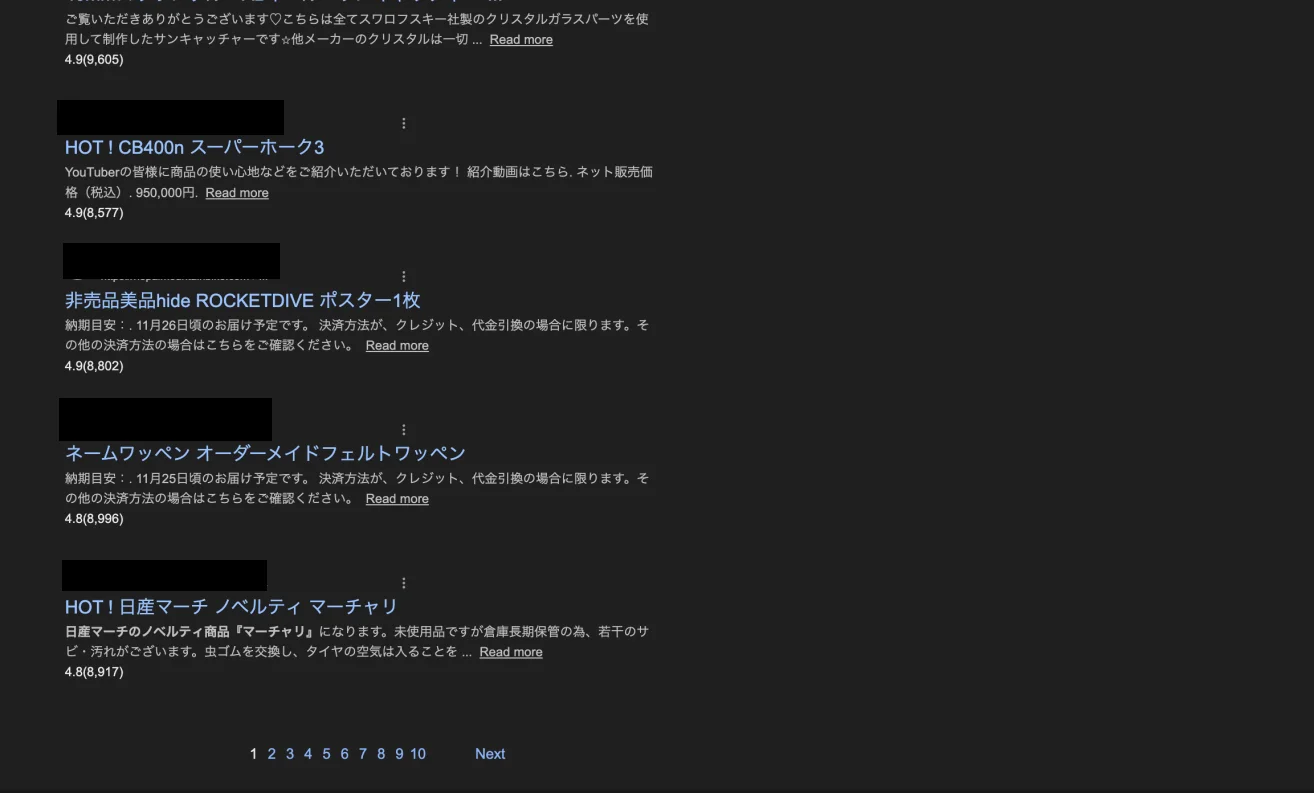
Japanese e-commerce listings, used electronics, crystal accessories, motorcycle parts, Afghan rugs, car wheels, all with yen pricing and thousands of fake reviews
-
Japanese fashion product pages (Ralph Lauren clothing, priced at ¥4,720 with 4.5-star ratings and 792 reviews

-
Vietnamese Chrome browser download pages
-
Celebrity gossip articles ("What Happened After Patrick Dempsey's Wife Jillian….")
The domain was being used as a general-purpose content farm, serving whatever the attackers needed indexed at any given time. Legitimate site pages were sitting in the same search results as Japanese retail listings, fake product reviews, and celebrity tabloid articles.
How the Attack Worked
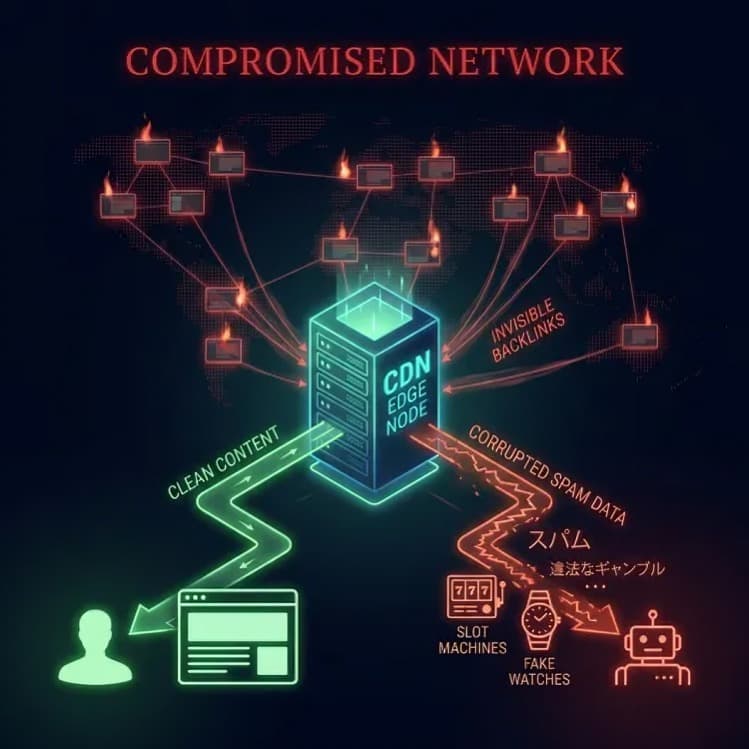
The attackers gained access to the Cloudflare account and deployed a malicious Worker file, a JavaScript script that runs at the CDN edge before requests ever reach the origin server.
The Worker did the following on every request:
-
Checked the incoming User-Agent string
-
If it matched a search engine bot (Googlebot, Bingbot, Naver's Yeti), it fetched a spam payload from a remote server and injected content just before the closing body tag
-
For all human visitors, it served the page completely untouched
This is why the infection was invisible to the site owner, developers, and any server-side security scanner. The origin server was never touched. The attack existed entirely only within Cloudflare's infrastructure.
A curl test with a spoofed Googlebot User-Agent string revealed the injected spam instantly at the bottom of the HTML output. No file on the server was modified. The attack left zero traces in the CMS.
The Backlink Network: Other Sites Were Victims Too
The injection was only half of the operation. The attackers had simultaneously compromised a large network of legitimate websites and used them to fire backlinks at the client's domain using gambling anchor text. None of those sites chose to link to the client. All of them had been silently hacked and enrolled into the same spam network without their knowledge.
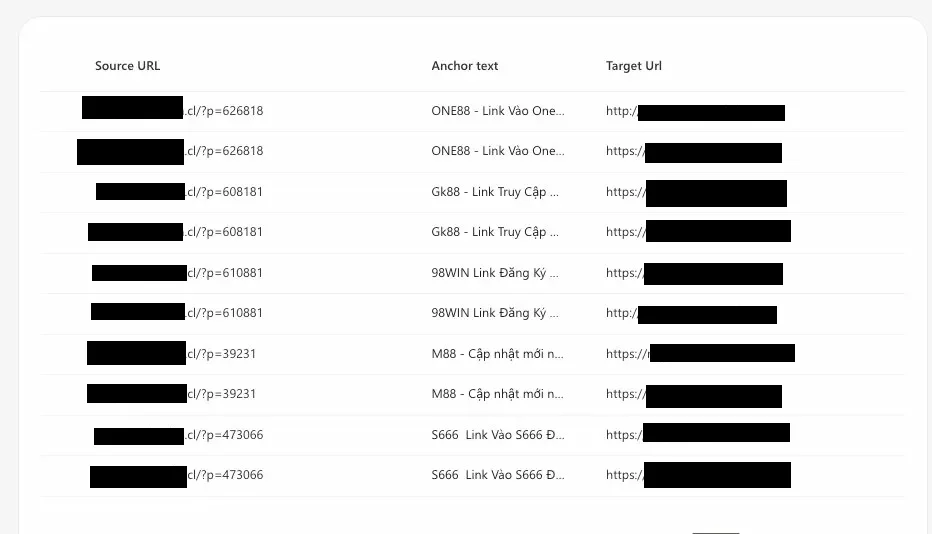
Over 2,500 backlinks were built this way across more than 20 compromised domains. The top sources included sites from Chile, Russia, the Czech Republic, French Polynesia, Belarus, Kazakhstan, and the UK. A Baptist church. A food market. A rail booking platform. None of them are gambling site. All of them were pawns.

The chain worked like this: hacked third-party sites pointed at the client's domain. The client's domain, via the injected Worker, pointed outbound to the gambling destinations, a relay of compromised legitimate domains laundering search authority toward the final target.
Resolving Steps:
-
Removed the unauthorized Cloudflare Worker from the Workers and Pages dashboard
-
Enabled 2FA and rotated all Cloudflare credentials and API tokens
-
Submitted a Disavow file to Google Search Console covering all spam linking domains
-
Redirected all hacked URLs to HTTP 410 Gone responses for all URLs Google had indexed with spam content
Google's Role in All of This
Google has known about this attack class since at least 2020. Sucuri documented it publicly. The technique is not new, not obscure, and not subtle. A spam network of this scale, firing thousands of links from hacked domains at unrelated sites with gambling and retail keywords, should be a pattern their systems recognise.
And yet it works. The client's domain was ranking for Vietnamese gambling terms. Japanese product listings were appearing under a site that has nothing to do with Japan or retail. The backlinks were being counted.
Google's official position is that its systems are good at identifying unnatural links, and that the Disavow tool exists as a recourse for site owners. But that shifts the entire burden of discovery and cleanup onto the victim. The site owner has to notice the anomaly, run the audit, build the disavow file, submit it, and wait weeks for it to take effect, all while the attackers continue to benefit.
Casino and retail spam of this kind continues to work for a few reasons. Google's crawler User-Agent is publicly documented, making it straightforward to serve it different content than human visitors. Legitimate domains with real history carry real authority, and acquiring that through compromise is cheaper and faster than earning it legitimately. The injection happens at the CDN layer, bypassing nearly every detection method available to a typical site owner. And the scale of the backlink network, spread across dozens of countries and domain types, makes it harder to flag as a single coordinated campaign.
Google has the data to see this at scale. Whether a hacked site in Chile is firing 634 backlinks at an unrelated site in Nepal using casino anchor text is not an ambiguous signal.
The question worth asking is why that is still enough to move rankings at all in 2026.
Reference: Sucuri, Abused Cloudflare Workers Service Used to Inject Korean SEO Spam (2020)

